Dependencies in Terraform and ARM Templates
- Terraform on Azure
- Deployments with Terraform and ARM Templates
- Modularisation of Terraform and ARM Templates
- Dependencies in Terraform and ARM Templates
- Terraform Calling ARM Templates
- Terraform with Azure DevOps: Setup
- Terraform with Azure DevOps: Key Vault Secrets
- Terraform Modules and Code Structure
- Terraform and Azure DevOps Tips and Tricks
Dependency Management
In order to determine the respective order of resource deployments and how it all fits together, we need to understand the dependencies that exist within our resources. This is a particular area of potential maintenance and complexity for our Infrastructure as Code (IaC) best efforts as we amend our deployment requirements over time. In this post we’ll look at how ARM templates and Terraform deal with the gnarly aspect of dependencies within resource deployments.
ARM Templates
Implicit Dependencies
References to Other Resource Properties
The ‘reference’ function can be used to reference properties from one resource for use within another. For example
"properties": {
"originHostHeader": "[reference(variables('webAppName')).hostNames[0]]",
...
}
The referenced resource must be a name of a resource defined within the same template. This creates an implicit dependency on the other resource. Passing Resource ID values in will not create an implicit dependency as ARM will not be able to interpret this.
List* Functions
The use of these within you template, as described at https://docs.microsoft.com/en-us/azure/azure-resource-manager/templates/template-functions-resource#list will also create an implicit dependency.
Linked/Nested Templates
When calling a linked/nested template, ARM will create an implicit dependency on the deployment that is defined within the linked template, essentially conducting the linked deployment first. This is an ‘all or nothing’ dependency, with no ability to define more granular resource dependencies across templates.
Explicit Dependencies using ‘dependsOn’
For all those resources that are defined within the same template that do not use ‘reference’ or ‘List*’ functions, ARM defines dependencies between resources explicitly using the ‘dependsOn’ attribute. An example of the use of the ‘dependsOn’ attribute is given below.
{
"type": "Microsoft.Compute/virtualMachineScaleSets",
"name": "[variables('namingInfix')]",
"location": "[variables('location')]",
"apiVersion": "2016-03-30",
"tags": {
"displayName": "VMScaleSet"
},
"dependsOn": [
"[variables('loadBalancerName')]",
"[variables('virtualNetworkName')]",
"storageLoop",
],
It is not possible to define dependencies across different templates in this manner. Managing these dependencies within each template is an element of the deployment definition that will need attention and can easily result in failed deployments when items are missed. This can add a considerable overhead to our efforts to get things managed via IaC for those deployments that have many resources.
Terraform
Implicit Dependencies
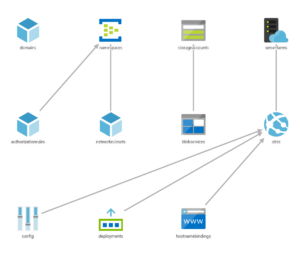
For all resources defined within the Terraform modules, both root modules and any referenced, Terraform will determine the dependencies and execute the resource management actions as needed. There is no need for explicitly declaring dependencies between resources, and as items are added/removed, so dependencies are adjusted as needed. When one resource depends on another it will be apparent from any referenced resource ids. This is essentially the same behaviour as for the ARM template ‘reference’ function, with the main advantage of Terraform being that these referenced resources can exist within separate modules/files.
Explicit Dependency Definition
One area where dependencies will need to be explicitly defined is where Terraform resource providers cannot be used for all resource aspects of the deployment required. Two common instances of this within Azure are:
- Execution of ARM Templates from Terraform using the ‘azurerm_template_deployment’ provider
- Ad hoc script execution (Bash, PowerShell, Cmd, Python etc.)
Terraform will be unaware of the resources actually deployed within an ARM template and as such will not be able to determine which other resources may depend on these. Likewise, actions undertaken within scripts and other executables will also present no known resource dependencies for Terraform to consider. In both these scenarios we need to state what our dependencies will be.
Explicit Dependencies using ‘depends_on’
Terraform allows the explicit defining of dependencies using the ‘depends_on’ attribute for a resource. In the example below, the dependency resources must all be deployed prior to this resource.
resource "null_resource" "exec_notebook_job_mount_workspace_storage_checkpointing" {
depends_on = {
null_resource.create_databricks_data_eng_cluster,
null_resource.add_workspace_notebook_storage_mount,
azurerm_storage_container.datalake
}
Null Resource and Triggers
Terraform provides a ‘Null Resource’ for arbitrary actions, being basically a resource definition for a non-existent resource. The ‘local-exec’ provisioner within this allows for the execution of various script types such as PowerShell, Bash or Cmd. ‘Triggers’ control the point at which this can be executed that define one or more prerequisite resources which must undergo change in order for the execution to take place. Using this approach we can execute any script or executable at a set point within the deployment. Note that these triggers act as logical ‘Or’ rather than ‘And’ triggers, so the resolution of any one of their resource conditions will allow the execution of the null resource.
resource "null_resource" "exec_notebook_job_mount_workspace_storage_checkpointing" {
depends_on = {
null_resource.create_databricks_data_eng_cluster,
null_resource.add_workspace_notebook_storage_mount,
azurerm_storage_container.datalake
}
triggers = {
create_databricks_data_eng_cluster = "${null_resource.create_databricks_data_eng_cluster.id}_${uuid()}"
add_workspace_notebook_workspace_storage = "${null_resource.add_workspace_notebook_storage_mount.id}_${uuid()}"
datalake_storage = "${azurerm_storage_container.datalake.id}_${uuid()}"
}
provisioner "local-exec" {
Note that there are multiple triggers that could set this resource to execute the respective script. All three of the related resources must however be deployed prior to executing the script, due to internal dependencies that the script has on these resources. As such we have used the depends_on block to ensure that all is in place beforehand.
Summing Up
Terraform makes dependencies a lot simpler to define than ARM templates. The combination of implicit dependency detection plus explicit definition where required allows for much easier definition of resource deployments. Being able to implicitly determine dependencies across files with Terraform also provides for less ‘structural constraints’ when writing the IaC definitions. This results in increased productivity and reduced management overhead. Administrators need think less about the order of deployment and can get on with defining the infrastructure, leaving the rest for Terraform.




About the author